storage security
What is storage security?
Storage security is the group of parameters and settings that make storage resources available to authorized users and trusted networks and unavailable to other entities. Storage security can encompass hardware management, application development, network security controls, communications protocols, organizational security policies, physical security and user behavior.
Storage security also includes a range of issues, including network security and cyberthreats. Protection must be provided against online threats such as viruses, worms, Trojans and other malicious code.
Why is storage security important?
Storage is where data resides. It is also where users and applications interact with data either directly or indirectly. An effective storage security strategy is essential in preventing unauthorized access to data and underlying storage systems. It is also important in ensuring authorized users have the access they need for their jobs.
Most organizations use multiple security measures as part of their access control efforts to prevent hackers or unauthorized users from accessing data. Even so, when an organization is attacked, storage security is often the last layer of defense against malware or other cyberthreats. That makes it even more important for IT teams to protect their storage systems.
However, storage security isn't an isolated effort. It must be part of a larger, organizationwide data management strategy that protects sensitive data from being compromised no matter where it resides.
Many enterprises use storage area networks (SANs) for data storage. When planning SAN security, IT teams should consider the following:
- The storage network should be easily accessible to authorized users and applications but difficult for hackers to compromise.
- The network should remain reliable and stable under a range of environmental conditions and patterns of use, without compromising security.
- Security mechanisms should protect against online threats, including viruses, worms, ransomware and other malicious code, without disrupting the network's stability and reliability.
Types of secure data storage and who is responsible
Data is stored primarily on local hard disk drives and solid-state drives, network-attached storage devices, RAID storage systems, cloud storage services and magnetic tape. Security measures, such as encryption and access controls, must be added to each medium to protect data from unauthorized access and other malicious attacks.
Within a data center, a data storage team is responsible for all aspects of data management, which includes storage security. Organizations that don't use a data center have a member of their IT team handle storage security issues.
Shifting storage activities to a cloud storage provider means that users must depend on the cloud storage security provided by the service and its security teams. When implementing a service-level agreement with a third-party organization, the SLA should address storage security.
Storage security management and methodology
Storage security management is the process of ensuring an organization's storage systems and data are fully protected in accordance with its security requirements. This includes data that resides within the storage systems, as well as data in transit to and from those systems.
Storage security management is broader than simply safeguarding the drives themselves. It must consider every attack vector that could lead to compromised storage systems and exposed data.
IT teams responsible for storage security must carry out several tasks to protect data resources, including the following:
- Encrypt sensitive data at rest and in motion and implement a secure encryption key management to ensure that data encryption is properly used.
- Disable unnecessary services to minimize the number of potential security holes.
- Apply updates and security patches to the operating system and other software regularly.
- Deploy network security that prevents unauthorized users from accessing storage systems and their data; this will also ensure endpoint security.
- Implement storage and data redundancy to prevent data loss in the event of a hardware failure, malicious activity or a natural disaster; this is especially important for data centers, cloud data and all other types of stored data.
- Inform users of the principles and policies that govern data, storage and network use.
The following criteria can help determine the effectiveness of a storage security methodology.
- The cost of implementing the system should be a small fraction of the value of the protected data.
- The cost to a hacker, in terms of money and real-time activities, to compromise the system should be more than the protected data is worth.
Common data storage security threats and vulnerabilities
There are many threats to an organization's data, ranging from malicious attacks to accidental data loss. Some of the more common threats include the following:
- Ransomware attacks. Ransomware is now one of the biggest threats to an organization's data. These attacks typically encrypt the target data to prevent a victim from accessing it. The victim must then pay a ransom for an encryption key to unlock the data. Ransomware infections occur as a result of clicking on a malicious link or opening an infected email attachment. Hackers have also been known to plant ransomware on storage devices. More recently, attackers have started to steal sensitive data as well as encrypt it, threatening to make the data public if the ransom isn't paid.
- Unauthorized access. Unauthorized data access typically involves a data breach in which a hacker or a rogue user gains access to an organization's sensitive data. The attacker might go after the data to sell it, disrupt operations, seek revenge or use it for political or competitive advantage.
- Unintentional access. Unintentional access can occur when a poorly constructed access control list accidentally grants users access to data they shouldn't be able to access. For example, this might happen because of overlapping group memberships.
- Data leakage. At its simplest, data leakage refers to sensitive data leaving an organization and making its way to the outside world. There are several ways in which data leaks occur. A user might copy data to a USB flash drive and walk out the door with that data. Similarly, users might email the data to someone inside or outside the company or even to themselves. Data leakage can also result from a user copying sensitive files to a consumer file-sharing service such as Dropbox.
- Accidental deletion or modification. Data can be lost if a user accidentally deletes or overwrites data that hasn't been properly backed up.
Data security vs. data protection
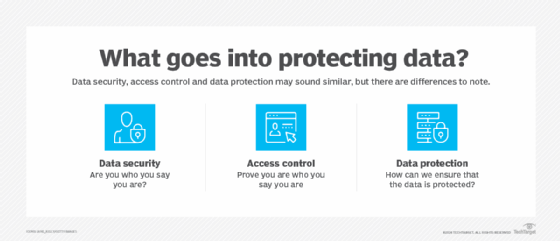
The term data security and data protection are often used interchangeably, but they refer to two different data management strategies.
- Data security focuses on preventing unauthorized access to an organization's data using mechanisms such as access control lists, storage encryption, multifactor authentication and cybersecurity software.
- Data protection concerns disaster recovery and putting into place mechanisms for backing up and recovering data. In this scenario, administrators create data copies that can be used to recover an organization's data following a storage infrastructure failure or other types of data loss events.
Although data security and data protection are two different concepts, they are related. For instance, if an organization is targeted by a ransomware attack, its data security might be able to stop the attack. But if the attack succeeds, the organization's data protection mechanisms -- its backup and restore processes -- can get the data back without paying the ransom, assuming the backups have not also fallen victim to the cyberattack.
If data protection is poorly implemented, it can create additional security risks. For example, an organization might back up its data to tape without encrypting the backups. An insider could steal the backup tape to gain access to the data.
Data security and compliance considerations
Organizations in regulated industries must examine any applicable compliance requirements when deciding how best to secure their data. Regulations such as the following focus heavily on data security and privacy:
- Health Insurance Portability and Accountability Act.
- Payment Card Industry Data Security Standard.
- California Consumer Privacy Act.
- European Union's General Data Protection Regulation.
Domestic and international standards for storage security must also be considered. Key standards include the following:
- ISO/IEC 27040:2024. This international standard defines physical, technical and administrative controls to protect storage systems, their associated infrastructures and the data stored within them.
- Storage Networking Industry Association. SNIA is a nonprofit global organization dedicated to developing standards and education programs to advance storage security and information technology.
- NIST SP 800-209 (2020) Security Guidelines for Storage Infrastructure. The National Institute of Standards and Technology Special Publication technical standard provides an overview of the development and evolution of storage technology, examines data storage security threats and delivers a detailed set of security recommendations and guidance to address storage threats.
Regulatory requirements vary, sometimes significantly. Nevertheless, they commonly establish mandates that govern how data should be stored. For instance, most regulations require all sensitive data to be encrypted. Many specify retention requirements.
Although the various regulations establish storage security requirements, they usually leave it up to the individual organization to choose the methods and mechanisms to use to meet those requirements.
Best practices for securing data
Entire books have been written on keeping data secure. Even so, there are several best practices that organizations should follow when protecting their storage systems and data.
- Establish and approve an enterprise-wide data storage and management policy. This policy specifies in detail the data and resources to be protected and the methods to ensure confidentiality, integrity and availability of data. It also defines the lifecycle of data, from inception to destruction, with considerations for security, storage options, transport, access, use, disaster recovery and business continuity.
- Identify where data is stored. Any data security initiative must specify where the organization's data resides. Organizations often have data that is stored both on premises and in cloud storage. This might include cloud-based object storage such as AWS Simple Storage Service (Amazon S3) and Azure Blob Storage or cloud service providers such as Dropbox Business and Microsoft OneDrive. Admins should also consider data on servers and desktops, in edge environments and locked away in other data repositories such as Iron Mountain.
- Classify the data. After locating the organization's data, administrators should categorize it based on sensitivity and application requirements. Some organizations skip data classification and treat all data as highly sensitive, whether or not it is. Although that approach makes data security easier, it can also lead to higher costs, degrade application performance and complicated data analytics.
- Protect sensitive data against leakage. IT teams should adopt a data loss prevention (DLP) system to guard against data leakage. Although DLP products vary in scope, most can detect sensitive data in outbound email messages. Such messages can then be intercepted -- and even silently forwarded to the appropriate department -- before being sent to the outside world. DLP products might also offer protections such as blocking access to USB storage devices.
- Audit access control lists. Access control lists determine who has access to particular resources. IT and security teams should periodically audit these lists to ensure no one has tampered with them. They should also check that users can access only the data they need to do their jobs.
- Implement multifactor authentication. Access control lists do little good if a user's account is compromised. One of the best ways to keep users from falling victim to stolen passwords is to implement multifactor authentication.
- Segregate administrative responsibilities. Allowing a single administrator to have full access to all IT systems is dangerous. If that administrator's account is compromised, an attacker can gain access to everything. This includes the storage environment, cloud computing resources and administrative controls. IT teams should use role-based access controls to delegate administrative responsibilities as-needed rather than granting blanket administrative privileges.
- Encrypt data at rest and in motion. All sensitive data -- whether on premises, in the cloud or in transit -- should be encrypted. Encryption keys must be carefully managed and protected.
- Practice good patch management. One of the best ways to prevent a data breach is to install software patches and firmware updates as they become available. These patches often address known vulnerabilities.
- Test and audit storage security measures. These activities ensure that stored data is securely protected from unauthorized access and that security controls are effective for storage requirements.
Artificial intelligence and object storage play a major role in data storage security. Learn how they figure into the top data storage security best practices.







